How to Analyze Thousands of Transactions During a Live Hack
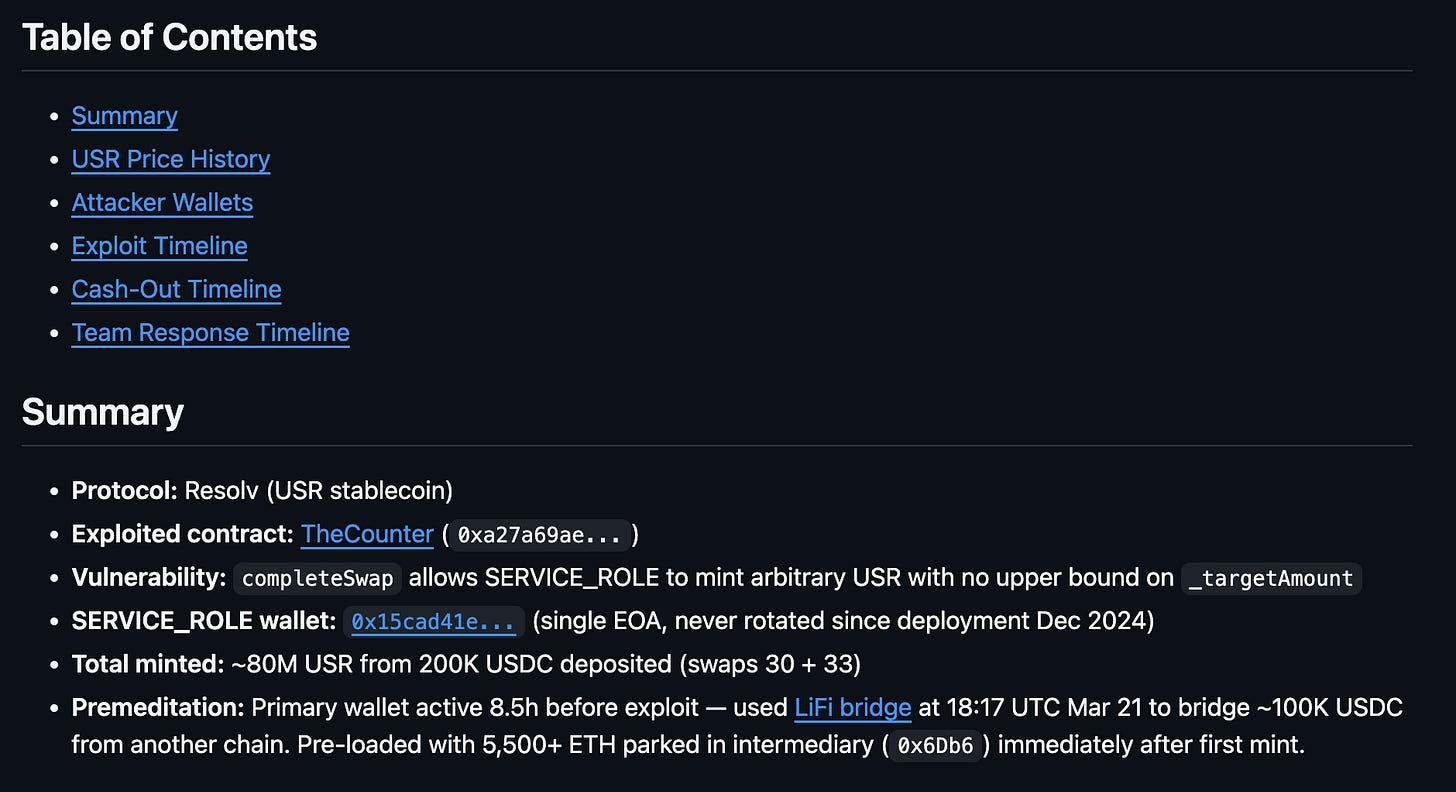
Resolv's USR stablecoin was hacked for $80m this weekend, and I was one of the first to analyze and monitor it because of Claude Code and Herd MCP.
When a critical event like a hack occurs, you don’t get the couple of hours or days you usually would to do analysis. Every minute counts - and you often start from not knowing anything about the contracts and watching the attacker's wallet(s) fire off dozens of transactions a second.
I’ll go over my workflow for creating this hack analysis and monitoring report in a GitHub Gist that’s updated every 5 minutes.
As soon as I saw the initial $50m mint, I opened Claude Code (which already had Herd MCP installed) and told it to analyze USR and tell me what caused the hack.
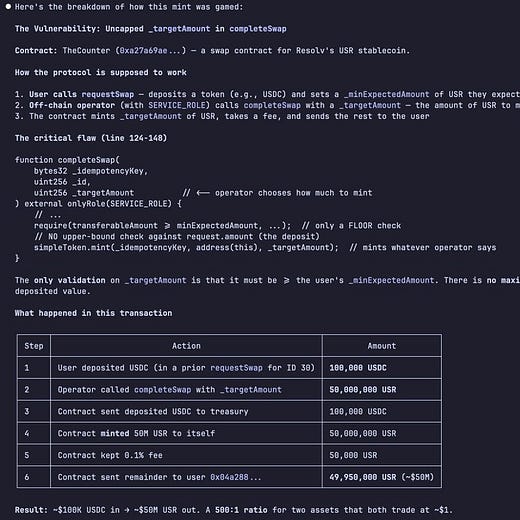
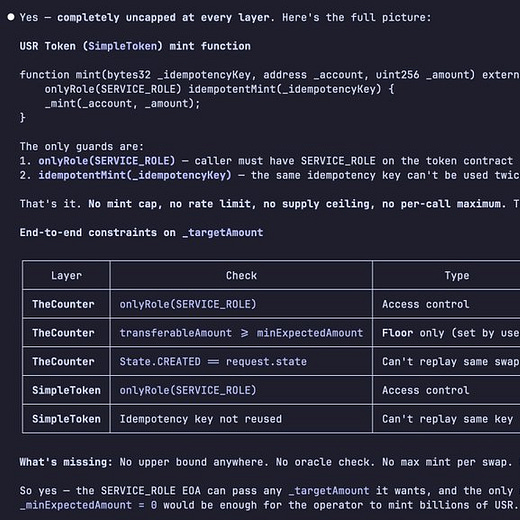
The hack was pretty simple (unfortunately, a team's private key was compromised), but it was still nice to understand it and find the related hack transactions within a minute. I immediately knew I wanted to monitor the attacker’s wallet for any further activity and to check the team’s multisig to see their responses.
The agent was able to track transfers to and from the attacker wallet to keep expanding the wallets to monitor, and it was also able to check across the USR contracts to find the team multisig and read the queued transactions.
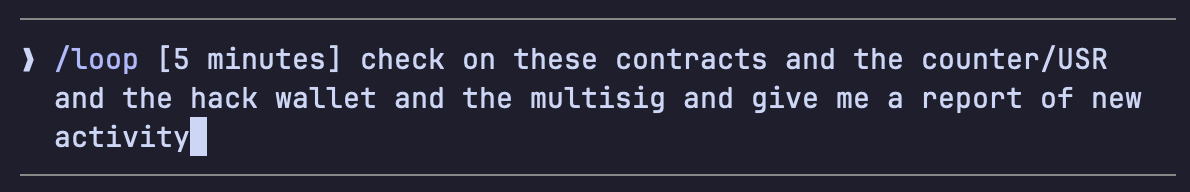
I immediately set this loop:
The initial report was now being uploaded to GitHub in a gist for me to easily read. Now, I could keep up with the activity and add things to the report as I did my own sleuthing alongside the agent.
You can read the gist yourself here; whenever I told Claude to add a new section, I would tell it to add and keep track of the methodology too. So for prices, I told it to check the spot price after each block of swaps, by reading traces data and querying onchain read functions.
This would have taken hours to do by hand, and I’m finding myself using AI to help with research and analysis in crypto more and more now.




super dope.
Any idea how many tokens, roughly, this endeavor consumed?
the speed advantage here is the part that matters. thanks for the take!